The SaaS Compliance Survival Guide: How to Stay Ahead in 2025
Dealing with compliance in SaaS isn’t just about checking off boxes. It’s legal obligations, risk assessments, cloud configs, encryption policies, and frameworks you’ve probably heard of but never actually read about.

First came the code. Then the customers. Now? The compliance docs. Honestly, this is where a lot of SaaS leaders hit a wall. They already have a product people want, and an excited sales team. But then someone in procurement asks if you’re SOC 2 certified, and the sweating starts.
Dealing with compliance in SaaS isn’t just about checking off boxes. It’s legal obligations, risk assessments, cloud configs, encryption policies, and frameworks you’ve probably heard of but never actually read about.
It’s not exactly what you imagined when you launched your product. But it’s part of scaling now, right alongside infrastructure decisions and pricing models. Because if you’re handling data, you’re handling risk. If you’re handling risk, someone, somewhere, is going to want proof you’re not making it up as you go.
The good news? You don’t need to become a compliance expert. You just need to understand what matters, what doesn’t, and how to stop running your entire risk program out of a Google Sheet called “compliance-stuff-v3-final.”
Compliance Is Not a Speed Bump: It’s a Sales Strategy
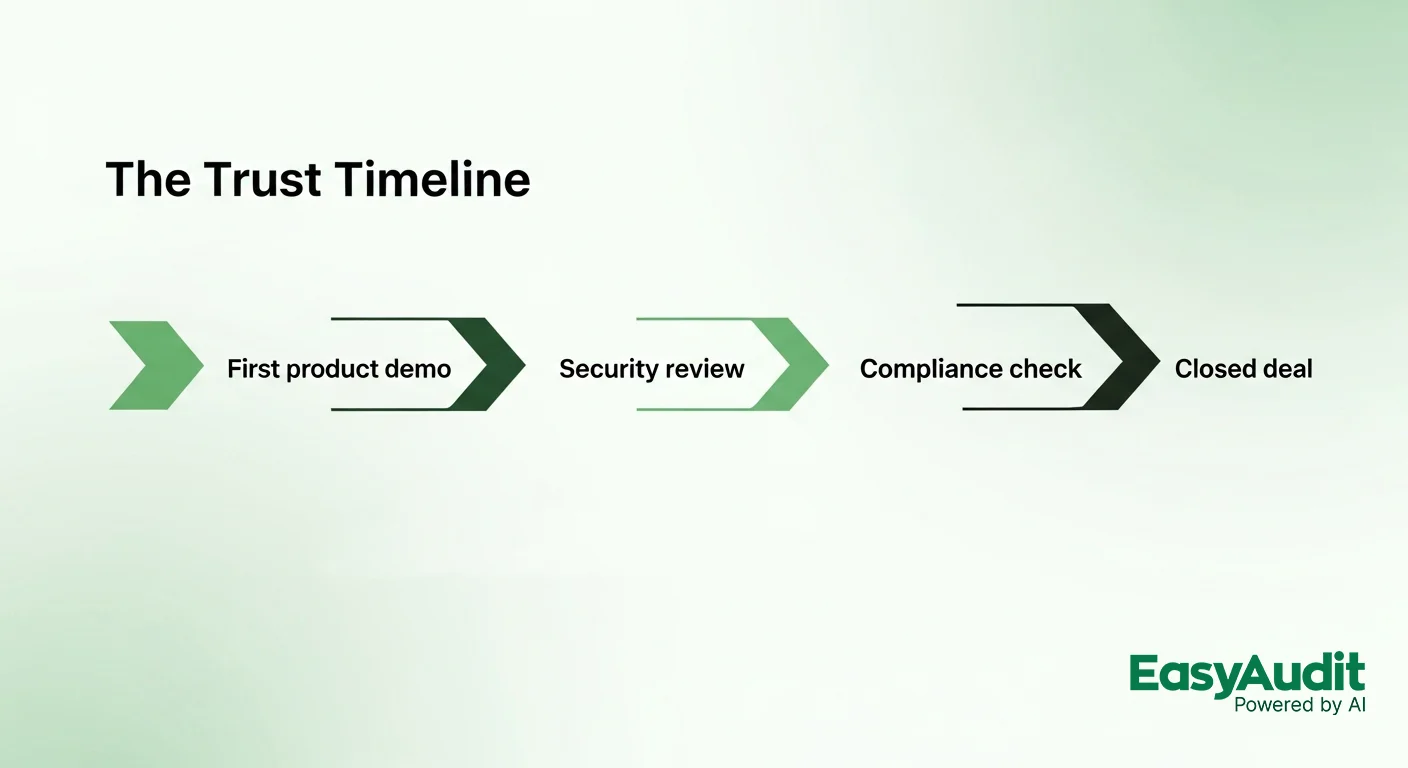
A funny thing happens once your SaaS product gets traction. Security reviews start landing before the contracts do. You’re not being judged just on features anymore. You're being asked how you store passwords. Who has access to logs. Whether your privacy policy matches your actual practice.
If you don’t have everything locked down (with evidence), you’re not just risking fines, you’re going to miss out on sales. Most buyers won’t say no because they think you’re insecure. They’ll say no because you can’t prove that you’re not.
Strong SaaS compliance management gives them that proof. Fast. It shows up in your maturity score, your documentation, and the way you answer their questions in two minutes instead of two weeks. That speed builds trust. That trust gets deals done.
This is why modern SaaS companies are investing in compliance strategies the way they used to invest in product features. The work you do here pays off across sales, renewals, audits, even investor due diligence. It’s not a checkbox, it’s leverage.
Especially if you’ve got the right tools. Platforms like EasyAudit take most of the grunt work off your plate. Real-time monitoring. Evidence collection. Policy mapping across frameworks. Stuff that used to require consultants and calendar chaos? Now handled before you even open your inbox.
When compliance is embedded in your stack instead of bolted on, it stops slowing you down. It starts pushing you forward.
The SaaS Compliance Jungle: What You’re Actually Up Against
The thing about SaaS compliance is, it doesn’t come with a welcome packet. No one hands you a cheat sheet when you launch. You find out what matters the same way everyone else does: when a customer asks, or when you almost lose a deal because someone flagged your missing SOC 2.
It’s messy at first, especially when you’re scaling. But once you get a sense of which frameworks apply to your product, things start to make more sense. The list below isn’t complete for everyone, but it covers the big ones. If you’re building anything that handles sensitive data, and these days, that’s most software, you’ll probably run into at least a few of these.
The Big Two Everyone Wants: SOC 2 and ISO 27001
Let’s start with the obvious one. If you’re selling to any business in the U.S., chances are, they want to see your SOC 2 report. It’s not a legal requirement, but it’s close enough. Buyers ask for it to prove you’re not winging it when it comes to security. It shows you have basic controls in place—like who has access to what, how you log things, and what happens if something breaks.
You don’t need to cover every trust principle right away. Most teams start with Security and Availability. That’s enough to pass procurement at a lot of companies. The key is showing that you’re consistent. If you say you do quarterly access reviews, the auditor is going to want to see proof. Not just a doc, but the actual logs.
ISO 27001 is SOC 2’s more formal cousin. Same idea: prove you have your act together, but more structured. ISO expects you to build an actual system around how you manage risk. Not just policies, but proof that you update them, assign ownership, and track compliance over time.
If you’re going global, ISO often opens more doors than SOC 2. Some teams go after both. Others pick the one their customers care about most.
NIST and CIS: For When You Need a Starting Point
Not every framework is about getting a certificate. Some just help you organize the chaos. NIST CSF is one of those. It gives you a way to structure your security program: how to identify risks, protect data, detect threats, respond to incidents, and recover after something breaks.
You won’t hang a NIST certificate on your wall, but that’s not the point. It’s a map, not a badge. Especially useful if you’re thinking about selling into government or regulated spaces.
Then there are CIS Controls. These are more tactical. Think of them as the shortlist of “stuff every SaaS team should be doing but probably isn’t.” Things like inventorying your assets, limiting admin access, enforcing MFA. It’s not fancy, but it’s a great way to cover the basics before you start chasing certifications.
Regional Privacy Laws: You Don’t Need an Office There to Be On the Hook
GDPR (Europe)
If you have a single user in the EU, GDPR applies. This law is serious, and enforcement is real. You’ll need to tell users what data you’re collecting, why, how long you’re keeping it, and who you’re sharing it with. You also need to give them a way to request their data or ask for it to be deleted. It’s not just about having a privacy policy. It’s about being able to back it up.
CCPA / CPRA (California)
California built its own version of GDPR, and it’s already been updated with stronger rules. These laws give people rights over their data, like opting out of tracking or asking who you’ve shared it with. If you’re serving U.S. users, assume someone from California is in there. This law has teeth now. The CPRA created an enforcement agency that’s active, and yes, they’ve issued fines.
PIPEDA (Canada), PDPA (Singapore), DPA (UAE)
You don’t hear about these as often, but they matter just as much if you’re operating globally. Canada’s PIPEDA is based on consent and reasonable data use. Singapore’s PDPA has similar expectations, focused on transparency and accountability. The UAE’s law is newer, but if you’re working in fintech or healthcare, you’ll see it in contracts.
EU Cloud Code of Conduct
This isn’t a law, but some companies in Europe expect to see it. It shows that your cloud services align with GDPR, even if you’re not based in the EU. Mostly useful when your buyers are very big or very regulated.
Industry-Specific Rules: Payments, Health, Finance, and Government Work
If you’re operating in a niche, like healthcare, payments, or public sector SaaS, some frameworks hit harder. These are the ones that tend to show up once you start landing bigger, more specialized clients.
PCI DSS
Touching credit card data? Even indirectly? You need to be PCI compliant. That includes how you handle card numbers, who can see them, how they’re encrypted, and how you log access. If you can avoid storing card data, do it. Offload to Stripe or Adyen and keep your scope low. But don’t assume that just using Stripe gets you out of PCI entirely. You still have obligations.
HIPAA / HITECH
Working in or near U.S. healthcare? You’ll need to follow HIPAA. This isn’t just for hospitals. If your platform touches patient data in any form, appointments, prescriptions, lab results, you’re in.
HITECH makes HIPAA even stricter when it comes to digital systems. You’ll need business associate agreements (BAAs), clear documentation, breach procedures, and a security program that can hold up under audit.
DORA
This is Europe’s new resilience law for financial platforms. If your SaaS product supports banks, insurance companies, or anything financial in the EU, you’ll need to align with DORA. This covers disaster recovery, incident response, and vendor management. This one’s just starting to hit, but the pressure is real.
SOX / MiFID II / IFRS
If you’re building software that supports financial reporting or investor disclosures, you might run into these. SOX governs public companies in the U.S., MiFID II hits capital markets in the EU, and IFRS is the global accounting standard. These aren’t your standard SaaS compliance items, but if your product touches numbers that end up in board reports, expect questions.
FedRAMP / FISMA
Want to work with U.S. government agencies? You’ll need FedRAMP. The process is long, expensive, and detailed, but once you’re certified, you’re eligible to land major contracts. FISMA is the broader law linked to government data. FedRAMP is the way cloud vendors prove they meet it.
SAMA
If you’re selling into the Saudi financial system, or the broader Middle East fintech scene, you’ll probably be asked about SAMA’s Cybersecurity Framework. It’s enforced, and if you’re not aligned, the conversation stops cold.
SS 584 / MTCS
This one shows up in Singapore. It’s a local requirement for cloud providers, especially if you’re working with the government or regulated sectors. There are three tiers, so check which level you fall into before answering that next security questionnaire.
Where SaaS Compliance Gets Messy
SaaS compliance isn’t hard because companies don’t care. It’s hard because everything moves faster than the rules do. Code ships daily. Vendors change monthly. Audits show up yearly, and somehow, you're supposed to tie all of it together.
These are the traps most teams fall into. They’re common. They’re costly. But they’re fixable.
1. The "Which Framework Do We Actually Need?" Spiral
You read three blogs and suddenly you think you need SOC 2, ISO, GDPR, PCI, and HIPAA. You don’t. But you do need to know what overlaps. That’s where tools like EasyAudit’s cross-framework mapping save your sanity.
2. Evidence Scavenger Hunts
Auditor: “Can you prove your access logs are complete for the last 90 days?”
You: “…Define ‘complete’?”
Manual evidence collection is where most compliance teams quietly unravel. Automate it. Seriously. Use a platform that knows what evidence you’ll need, and collects it before anyone asks.
3. Cloud Chaos
Multiple environments. Dozens of third-party apps. Two ex-engineers with persistent admin access. It adds up. Fast. Asset management and access control are still top causes of SaaS compliance failure.
4. Policy Theater
Having a document named “encryption-policy-v2-final-really-final.pdf” does not mean you’re compliant. If you’ve never read it, your team isn’t following it, and it hasn’t been updated since the intern wrote it in 2021, it’s not worth much.
5. One Person Owns It. And They're Drowning
In a lot of early-stage SaaS teams, compliance lands on someone who “kind of” knows security. They care. But they don’t have time. Or help. Or budget. That’s not sustainable. You need real ownership, smart tooling, and clear accountability.
The 7-Step SaaS Compliance Survival Plan
You’ve figured out which regulations apply. You know where the mess lives. Now comes the question every SaaS team eventually asks: “How do we start doing this for real?”
You don’t need 15 consultants or a binder of policies nobody reads. What you do need is structure. And some smart automation. And maybe one less Slack thread titled “do we have that policy somewhere?”
Here’s how you build a SaaS compliance strategy that doesn’t fall apart the moment someone opens a security questionnaire.
1. Know Your Stack, Know Your Risk
Before you can protect anything, you need to know what you’re working with. What systems hold sensitive data? Who has access to what? Which vendors are still active? (Looking at you, legacy analytics tool from 2019.)
Create a simple map of your infrastructure. Label where data flows, where it’s stored, who can touch it, and what’s exposed to the internet.
Tools like EasyAudit’s Risk Assessment can do most of this automatically. They scan your cloud setup, flag anything weird, and help you build a clear picture. What used to take days of interviews and diagrams now takes minutes.
2. Pick the Right Frameworks, Not All of Them
You don’t need every badge. You need the ones that make sense for your product, your customer base, and your market.
Selling to US businesses? SOC 2.
EU users? GDPR.
Handling payments? PCI DSS.
PHI? HIPAA.
International scale? ISO 27001.
Instead of building five separate compliance programs, use something like EasyAudit’s Framework Cross-Mapping to map controls across standards. One policy, many boxes checked.
3. Write Real Policies (Not Just for Auditors)
This is where most teams fake it. You find a template, replace the company name, slap it in a folder, and hope nobody asks questions.
That doesn’t work anymore.
Your policies need to match what your team actually does. They should be versioned. Easy to find. Easy to follow. They should evolve with your product, just like your code.
Platforms like EasyAudit generate these automatically, based on your infrastructure and frameworks. They aren’t just boilerplate. They’re mapped, auditable, and editable, so you don’t have to pretend “policy” is a fancy word for Word docs.
4. Stop Collecting Evidence Manually
If someone on your team is still screenshotting the AWS console and pasting it into a folder called “evidence,” please buy them coffee. Then retire that process immediately.
Evidence should collect itself.
Smart platforms plug into your stack and pull what you need as you go. Not just raw logs, but versioned proof, tied to the right control, with context included. That’s how EasyAudit’s Document-to-Control Mapping works, and auditors love it.
5. Monitor Everything Constantly
Controls drift. Permissions creep. People forget to update things. Real-time monitoring isn’t just nice to have. It’s the only way to know if your program is still intact between audits.
Set alerts for expired certs. Flag access changes. Watch for control failures. If you can’t do this in real time, you’re already behind.
EasyAudit’s Continuous Monitoring catches these issues before they land in the auditor’s inbox—or worse, the news.
6. Make Compliance a Team Sport
One overwhelmed ops lead cannot own your entire compliance posture. It touches engineering, security, legal, product, even sales. You need clear ownership. Role-based dashboards. Shared visibility.
This isn’t about more meetings. It’s about fewer surprises.
Build workflows into your tools. Integrate checks into CI/CD. Set reminders. Use automation. Let each team handle their slice of the pie.
7. Remediate Fast, Document Faster
When something breaks, you don’t just need to fix it. You need to log it, explain it, prove it’s resolved, and show how you’ll prevent it in the future.
EasyAudit’s AI Compliance Officer doesn’t just tell you what’s wrong. It tells you why, where it maps, and what to do next. You’re not chasing issues. You’re getting context, resolution steps, and audit-ready documentation in one place.
Combining SaaS Compliance with Security
Once, compliance teams and security teams were like neighboring planets. Close enough to see each other. Too far apart to actually collaborate. One side wrote policies. The other fought fires. Every so often, they’d meet during an audit, stare across the table, and agree silently that both were probably underpaid.
But that’s changing.
In today’s SaaS world, security and compliance management are merging. Not because someone made a nice speech about alignment. Because they have to. When your infrastructure lives in the cloud, your policies touch every container, every identity, every permission. If your controls are out of date, your security is too. If your logs are incomplete, so is your compliance report.
Modern companies get this. They’re building platforms, not paper trails. They use shared dashboards, shared tooling, shared alerts. They treat SaaS compliance standards like living systems, not documents filed away somewhere under Legal.
When these two worlds connect, everything gets faster. Control failures are caught earlier. Risk gets mapped automatically. Audits become less of a panic and more of a formality.
Platforms like EasyAudit sit right in the middle of this merger. Real-time compliance monitoring feeds straight into security observability. AI-driven alerts flag both risk and policy violations. The same system that proves you’re compliant is also the one showing you what broke, and what might break next.
Why SaaS Companies Are Choosing EasyAudit Over Chaos
There are two kinds of SaaS companies.
The first is duct-taping together compliance from shared folders, Notion checklists, half-written policies, and screenshots that may or may not be from the right environment. This company might survive for a while. But one security questionnaire, one due diligence round, one angry auditor, and everything collapses.
The second company does things differently. They automate where it matters. They monitor continuously. They know what frameworks they need, and they don’t waste time duplicating effort. They don’t just react to compliance pressure. They’re ready for it.
EasyAudit was built for the second company.
Here’s what it delivers:
AI-powered compliance tools that understand your business, your frameworks, and your infrastructure
Continuous Monitoring that doesn’t just alert you, it explains what’s wrong and how to fix it
Custom Control Generation that tailors policies to your real setup (no more copy-paste PDFs)
Cross-Framework Mapping so you don’t repeat the same controls 12 different ways
Automated Evidence Collection that pulls from your stack and maps everything to the right control
Real-Time Dashboards that show your compliance posture in one view across SOC 2, ISO, HIPAA, GDPR, and more
It’s how SaaS teams grow, close deals faster, and walk into audits without anxiety. Because enterprise SaaS compliance shouldn’t feel like a second job. It should be baked into the product, just like your logging, your billing, or your CI pipeline.
The Future of SaaS Compliance
SaaS compliance isn’t heading toward simplicity. It’s heading toward velocity. Frameworks are evolving. Regulators are waking up. Customers are expecting real-time transparency.
Here’s a snapshot view of what’s coming next:
Continuous Everything: Audits used to happen once a year. That made sense when systems barely changed. Now, your codebase changes daily. Your infrastructure changes weekly. Waiting twelve months to check your controls? That’s asking for trouble. SaaS compliance strategies in 2025+ will rely on real-time visibility, constantly.
Explainable AI, Even in Compliance: As more companies bake AI into their platforms, regulators are starting to ask how that AI makes decisions. That means audit trails, transparency, fairness checks, even for your internal tools.
Compliance by Design: You know how “security by design” became a thing? Compliance is going the same route. Instead of reacting, companies are starting to build it into their dev workflows, CI/CD pipelines, even design reviews. This shift is huge. It turns SaaS compliance into infrastructure, not overhead.
Global-by-Default: One user in Berlin? You're under GDPR. One client in California? CCPA. Selling to the UK? DPA and UK-GDPR. Even small companies need SaaS compliance standards that flex by location. That’s why region-aware controls and multilingual policies are essential.
Trust as a Feature: compliance isn’t just about staying out of trouble anymore. It’s a sales feature. A retention lever. A trust signal your next customer is actively looking for. The companies that get this right? They don’t scramble to pass audits. Their systems already know if they’re passing.

SaaS Compliance That Actually Works
You’ve got the product. You’ve got the customers. Now it’s time to build the trust.
SaaS compliance is about creating systems that scale responsibly. It’s about protecting the people who use your product, the team that builds it, and the business that depends on it. Most importantly, it’s about doing it without burning out your engineers or turning your ops team into amateur lawyers.
That’s where tools like EasyAudit pay off. They don’t just help you check boxes. They help you build systems that hold up, under audits, under scrutiny, under growth.
You don’t have to guess which policies you need. Or chase evidence through six Slack threads. Or dread every compliance email that lands on a Friday afternoon.
With the right strategy, and platform, you don’t just survive compliance, you own it.
Ready to get started? Book a demo here.
FAQs
What is SaaS compliance, really?
It’s the set of controls, policies, and processes your SaaS company uses to prove you're handling data securely, responsibly, and in line with laws or customer expectations.
Do we need to be SOC 2 certified to sell to businesses?
Probably, yes. If you’re B2B, especially in the US, SOC 2 is the minimum bar most buyers expect. Without it, deals will take longer or disappear entirely
What’s the deal with PCI compliance for SaaS?
If your app touches credit card data, you may have obligations under PCI DSS. Encrypt data. Secure your network. Follow their control list. Better yet, let EasyAudit tell you where you stand.
Is GDPR just for EU companies?
Nope. If even one user is in the EU, GDPR applies. That means consent, data rights, and breach notification requirements. Same goes for CCPA in California.
Can we automate our SaaS compliance checklist?
Yes. That’s kind of the point. Modern tools like EasyAudit automate evidence collection, policy mapping, control monitoring, and risk assessments across frameworks.